FBI and CISA Guidance on Destructive Malware

It is well known that malware can disrupt the availability of critical assets and data, impairing an organization’s ability to operate. It is key that organizations remain vigilant and defend against malware across all potential entry points.
Recently, the United States Cybersecurity and Infrastructure Security Agency (CISA) and Federal Bureau of Investigation (FBI) released a joint cybersecurity advisory to raise awareness regarding destructive malware and provide preventative recommendations.
The advisory pointed out that within the first two months of 2022, sophisticated malware operations identified as WhisperGate and HermeticWiper were launched to shutdown Ukrainian computer systems, that additional cyberattacks are anticipated, and that such threats could “spill over to organizations in other countries.”
|
Actions to take today:
|
“Destructive malware may use popular communication tools to spread,” the advisory states, “including worms sent through email and instant messages, Trojan horses dropped from websites, and virus-infected files downloaded from peer-to-peer connections.”
While the cloud inherently provides a level of security, there has been evidence of cybercriminals maintaining persistent, long-term access in compromised cloud environments.
With heightened security concerns due to increased nefarious activity related to geopolitical events, the CISA and FBI underscore the importance of proactively following best practices for defending against malware. The following is a high-level overview of some of the preventative recommendations presented in the cybersecurity advisory:
Communication Flow
- Segment networks
- Permit connectivity via the minimum scope of ports and protocols
- Contain systems that can be used as a gateway to pivot or directly connect to endpoints
- Ensure that centralized network and storage devices’ management interfaces reside on restrictive VLANs
Access Control
- Require multifactor authentication
- Only allow authorized users to directly access or authenticate to systems that interface with multiple endpoints
- Use unique domain accounts for each enterprise application service; apply least privilege
- Deny service accounts permission to access network shares and critical data
- Do not allow elevated permissions to accounts that are used to authenticate to centralized enterprise application servers/devices
- Restrict Write/Modify/Full Control permissions when possible
Monitoring
- Collect and review security logs and network flow data for anomalous activity (e.g., multiple failed authentication attempts)
- Log and audit all configuration changes
File Distribution
- Stagger patches or AV signature distributions
- Ensure updates are from trusted sources
- Check file and data integrity
- Monitor and audit data that is distributed from an enterprise application
System and Application Hardening
- Maintain robust vulnerability management and patching practices; automate and test
- Configure and harden based upon industry-standard and vendor best practices (e.g., apply role-based access control and bar users from disabling AV)
Cloud Storage: An Unsuspected Attack Vector
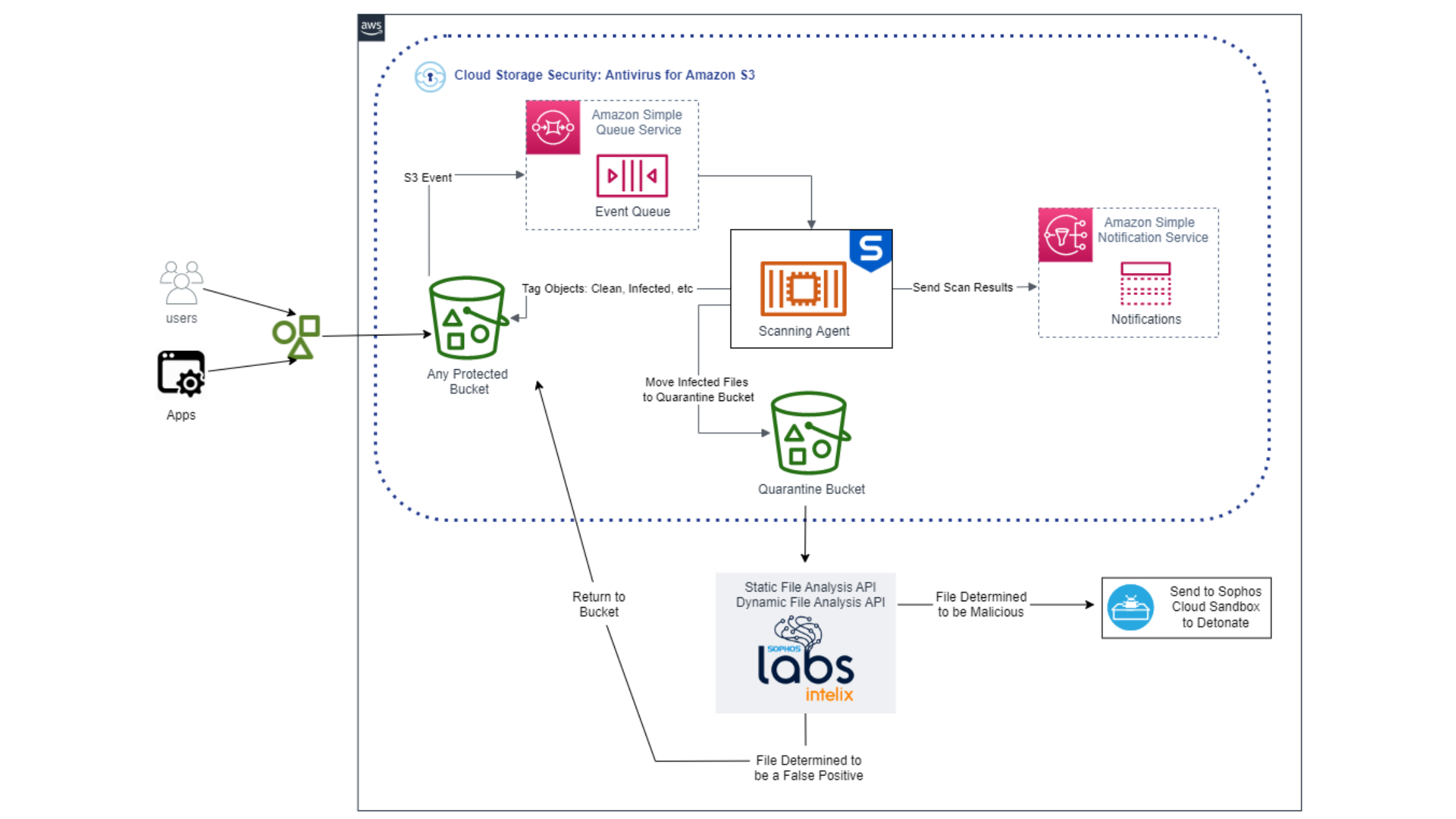
Proper configurations as well as scanning for viruses and malware is critical to preventing the transmission of advanced threats. In addition to applying the configuration guidance above, it’s important that the cleanliness of files and data in cloud storage isn’t overlooked, especially if that content is generated from third parties.
Cloud Storage Security helps organizations answer questions such as "Which buckets have secure permission policies?", "Do I have publicly accessible buckets?", "Do I have files containing malware?" and more.
Ensure proper access and stop the spread of infection with Antivirus for Amazon S3 by Cloud Storage Security. Learn more or scan up to 500 GB for free with a 30 day trial on AWS Marketplace.